
Cybersecurity
Solutions
Reduce the risks induced by the Digital Transformation; discover our Cybersecurity solutions
Cybersecurity is a critical challenge for businesses of all sizes. Cyberattacks are increasingly frequent and sophisticated, threatening operations, data, and reputation. Protecting your organization requires tailored cybersecurity solutions. As digital technologies like Cloud, IoT, and remote work expand, cybercriminals exploit system flaws and employee vulnerabilities, making robust security essential to ensure business continuity and resilience.
Get inside the
head of a hacker
Cybersecurity Facts and Statistics
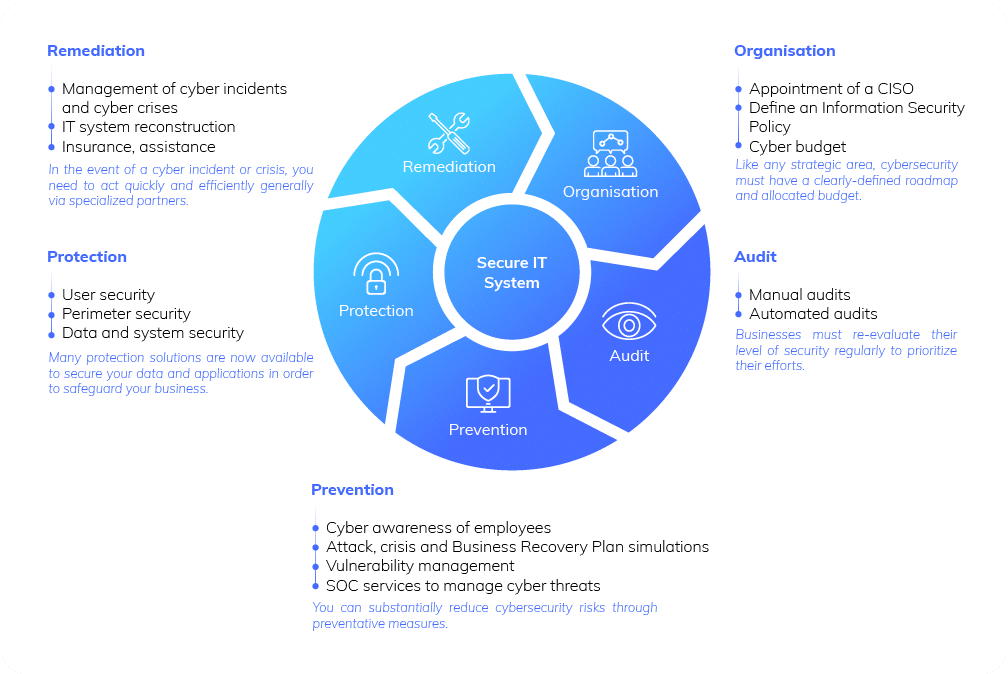
The 5 Pillars of Cybersecurity
Prodware Cybersecurity
Solutions and Services
With the digital transformation also comes the increased risk of exposed IT systems and thus more cyber threats. To help businesses manage their cyber risks, Prodware has developed a large portfolio of services from a part-time CISO (Chief Information Security Officer) to a full-time SOC (Security Operation Center) to manage your cyber risks 24/7. To complete these services, Prodware has fostered a network of strategic partnerships with top leaders in the security industry including Microsoft, which offers a vast security ecosystem for both Cloud infrastructures and On Premise.
Governance
and Compliance

Part-time CISO
Provision of an experienced Chief Information Security Officer to lead your Cybersecurity strategy and ensure the integrity of your Information System against internal and external risks.

Security committee
Through regular committees, your dedicated operations manager collects and analyzes your KPIs and security incidents as part of a continuous process of improving security.

ISP (Information Security Policy) development
Define and structure the Information Security Policy for your organization.

Audit Services

Infrastructure, data, collaborative tools and Dynamics software audit
Analysis of the levels of security in place and proposals of detailed action plans.

Penetration testing (ethical hacking)
Penetration tests carried out by ethical hackers to pinpoint your human and technical weaknesses so that they can be corrected.

Users and devices

Managed Services
Our Secure Workplace contract is a turnkey outsourcing service for managing your employees and your IT assets. It supports your terminals and servers, your Microsoft collaborative tools and provides all the required governance and security services to make your organization safer and more efficient.

Perimeter Security

Network segmentation
Partitioning of IT assets in separate networks to limit the risks in the event of an attack.

Systems and Data
Discover a few of our Cybersecurity solutions
Why choose Prodware?
Cybersecurity is a major concern for all businesses. As a digital transformation partner, Prodware also supports its customers in strengthening their cybersecurity strategy by ensuring the security of their infrastructure, professional applications, data and by offering protection services against cyber risks.












































